The Enemy Within: Protecting Your Business from the 'Disgruntled Delete'
Listen to the introduction of this article.
You've got firewalls. Antivirus. Multi-factor authentication. You're locked down against hackers halfway around the world.
But what about the person sitting three desks down who just got their termination notice?
The Threat You're Not Planning For
Most business owners obsess over external threats. Ransomware gangs. Phishing attacks. State-sponsored hackers. They spend thousands on perimeter security while completely overlooking the most dangerous vulnerability in their infrastructure.
Their own employees.
Here's what the data shows: 77% of organizations have experienced insider-related data loss in recent years. Not might experience. Have experienced. And the financial impact isn't trivial: internal breaches cost millions on average, with a single incident easily exceeding $600,000 in direct costs, lost productivity, and recovery expenses.
The problem runs deeper than most executives realize.

Two Flavors of Disaster
Internal threats come in two varieties, and you're vulnerable to both.
The first is malicious. The disgruntled employee who got passed over for promotion. The admin who just received a termination notice. The contractor who feels undervalued. These individuals have legitimate access, deep system knowledge, and a window of opportunity to cause serious damage before they walk out the door. They can delete files, steal customer data, sabotage systems, or simply take proprietary information to a competitor.
This accounts for about 25% of insider incidents.
The second is accidental. The well-meaning employee who clicks the wrong button. The tired admin who runs a script in production instead of testing. The new hire who doesn't understand the backup system they just reconfigured. These people don't mean harm, but the damage is identical.
This accounts for the other 75%.
Both scenarios end the same way: your data is gone, your systems are compromised, and you're scrambling to recover. The difference is intent, but the outcome is identical.
Why Traditional Security Fails Here
Your firewall doesn't stop someone with a valid username and password.
Your antivirus doesn't flag a database export initiated by an authorized administrator.
Your intrusion detection system doesn't trigger when someone with legitimate access deletes a file share.
Traditional security tools are built to stop outsiders from getting in. They're not designed to stop insiders who are already in. And that's the gap that causes catastrophic data loss.
Consider the typical scenario: An employee receives their two-week notice on Friday afternoon. By Monday morning, they've downloaded client lists, financial records, and strategic plans. By Wednesday, they've accepted a position with your competitor. By Friday, they walk out with your business intelligence in their pocket.
Your security system saw nothing wrong. Every login was legitimate. Every file access was authorized. Every download was within their permissions.
The breach was invisible because it looked like normal work.

The Core Solution: Immutability and Separation of Duties
The fix isn't more monitoring. It's not behavior analytics or machine learning algorithms trying to detect "suspicious activity."
The fix is removing the ability to cause permanent damage in the first place.
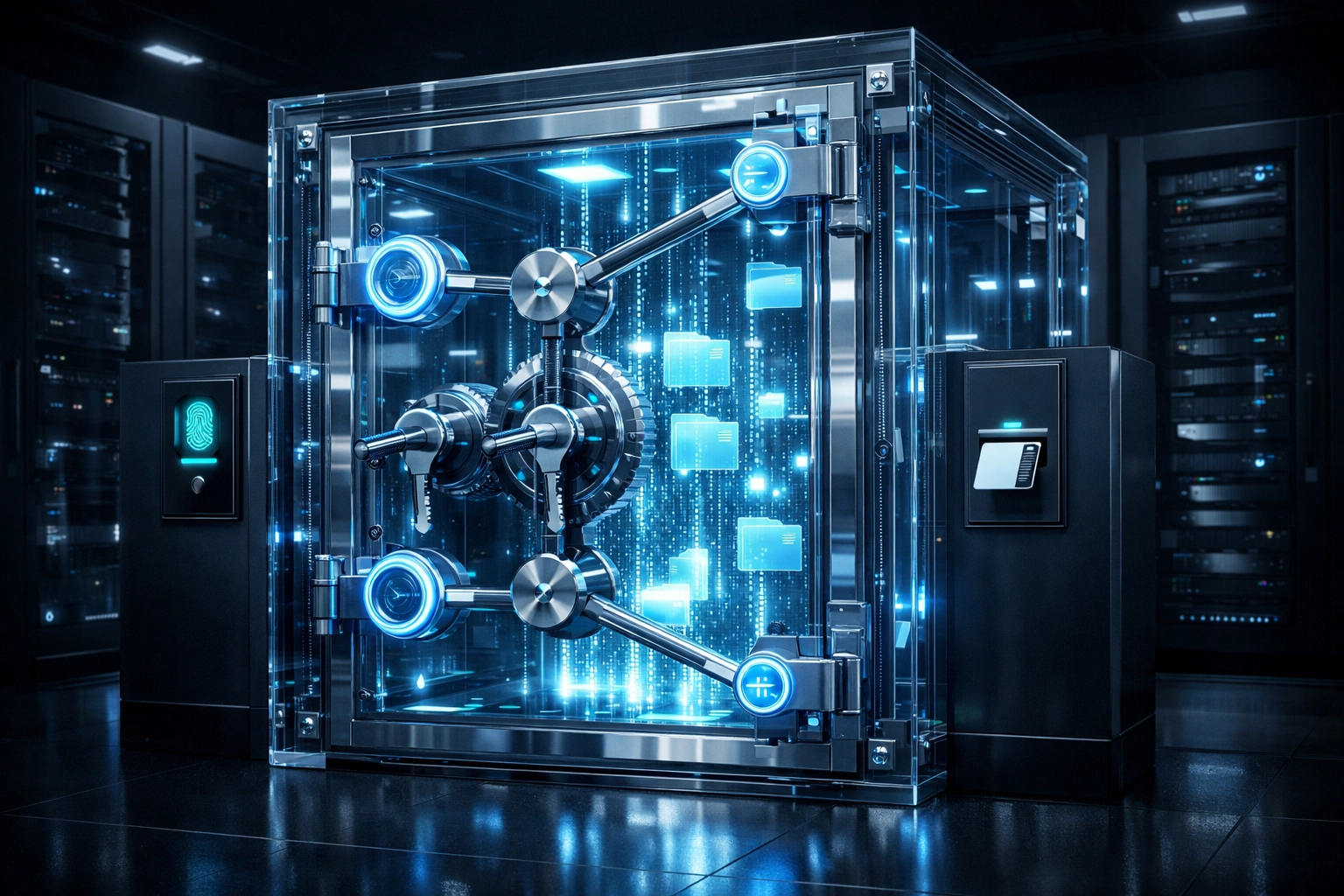
Immutable backups create a time-locked vault that no one: not administrators, not owners, not anyone: can delete or modify once written. Even if someone with full system access decides to scorched-earth your entire infrastructure, your backup data remains untouchable for a predetermined retention period. Learn more about immutable backups.
This isn't about detecting the threat. It's about making the threat irrelevant.
But immutability alone isn't enough.
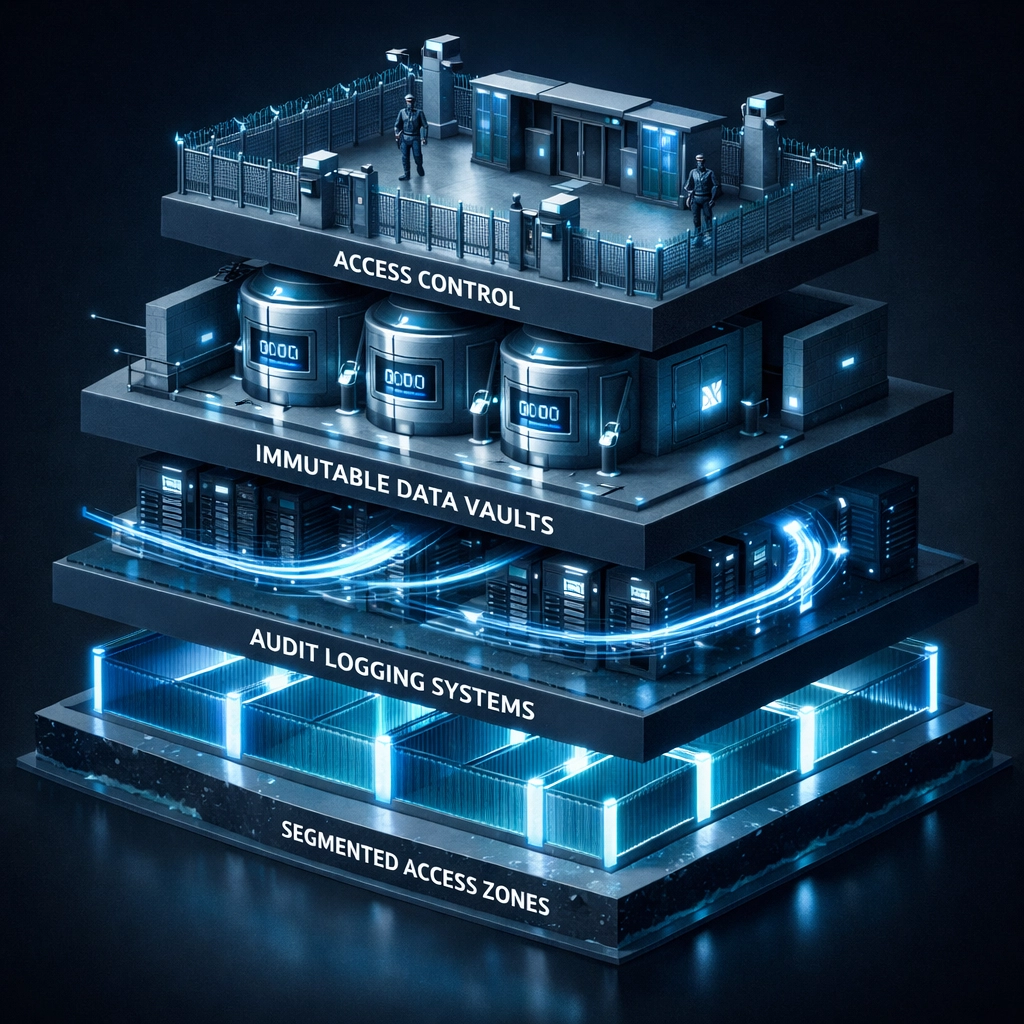
Separation of duties ensures that no single person can compromise your entire backup infrastructure. In military operations, this is called two-person control. Nuclear launch codes require two keys. Classified access requires two authorizations. Mission-critical systems don't have a single point of failure.
Your backup infrastructure should work the same way.
One person configures the backups. Another person monitors them. A third person tests restores. No single employee: no matter how trusted, no matter how senior: should have unilateral control over your ability to recover from disaster.
This isn't about trust. It's about system design.
The BAIFRONT Way: Veteran Methodology Meets IT Infrastructure
As a veteran-owned business, we approach data protection the way we approached mission planning: assume every point of failure will fail, and build systems that work anyway.
In military operations, you don't hope your equipment works. You verify it. You don't assume your team is reliable. You create redundancy. You don't trust that everything will go according to plan. You prepare for the worst-case scenario and build upward from there.
That same discipline applies to backup infrastructure.
We design systems with no single point of failure: not in hardware, not in software, and not in personnel. Your backup infrastructure shouldn't be vulnerable to a single compromised account, a single malicious action, or a single catastrophic mistake.
Here's what that looks like in practice:
Access segmentation. Administrators who manage production systems don't have administrative access to backup systems. The person who can delete a file share can't delete the backup of that file share.
Time-locked immutability. Once backup data is written, it's protected for a minimum retention period: typically 30-90 days depending on your requirements. Even if someone compromises every account in your organization, they can't touch that data.
Restore verification. We don't just assume backups work. We test them. Regularly. In isolated environments. With documented results. Because a backup you can't restore is just expensive storage.
Audit logging. Every access, every change, every restore attempt is logged and monitored. If something goes wrong, you have a complete record of what happened and when.
This isn't paranoia. It's operational readiness.
What This Looks Like in Real Terms
You hire a new IT administrator. They're competent, experienced, and trusted. Six months later, they're served with divorce papers. Two weeks after that, they're visibly angry at work. A week after that, they're terminated for poor performance.
In a traditional environment, that's a catastrophic vulnerability window. They have access. They have knowledge. They have motive.
In a properly designed system, it doesn't matter.
They can't delete the backups because they don't have immutable delete permissions. They can't modify the backup configuration because separation of duties means they only control one piece of the infrastructure. They can't cover their tracks because every action is logged independently.
Or consider the accidental scenario: Your senior administrator is working late, exhausted from a 14-hour day dealing with a production outage. They run a cleanup script to clear temporary files. The script has a typo. Instead of deleting /tmp/old_logs, it targets /data/customer_files.
Within seconds, years of customer data are gone.
In a traditional environment, you're hoping your backups work. You're scrambling to find a restore point. You're praying you can recover.
In a properly designed system, you're executing a documented restore procedure. The immutable backups weren't touched by the deletion. Your RTO and RPO are known quantities because you test them regularly. Recovery is a process, not a panic.
Implementation: Where to Start
If you're reading this and realizing your infrastructure doesn't have these protections, you're not alone. Most businesses discover these gaps only after a disaster.
Here's the immediate action plan:
- Audit your current backup access. Who can delete backup data? Who can modify retention policies? Who has administrative control over your backup infrastructure? If the answer is "one person" or "everyone with admin rights," you have a critical vulnerability.
- Implement immutability now. This is non-negotiable. Your backup data should be write-once, read-many (WORM) with time-locked retention. It's not a nice-to-have. It's baseline protection.
- Separate duties immediately. No single person should control both production systems and backup infrastructure. If that's your current state, start creating separation today.
- Test your restores. Not the backup job status. The actual restore. In an isolated environment. With verification that the data is complete and usable.
- Document everything. Who has access to what. What the restore procedures are. What the RTO and RPO targets are. Documentation turns chaos into process.

Your Next Step
The enemy within isn't always malicious. Sometimes it's just human error on a bad day. But the result is the same: your data is gone, and you're racing to recover.
The solution isn't hoping it doesn't happen. It's building systems that can't be destroyed by a single person, a single mistake, or a single malicious action.
BAIFRONT's Tier 1 Free Comprehensive Assessment identifies exactly where your infrastructure is vulnerable to insider threats: both malicious and accidental. We analyze your backup access controls, test your immutability implementation, verify your separation of duties, and document gaps that could cost you during a crisis.
No sales pressure. No lengthy commitments. Just a clear assessment of where you stand and what needs to change.
Because the best time to discover these vulnerabilities is before someone exploits them.